VPN Protocols Review
Keeping your information safe whether it’s for business or personal use, is important and as everything moves online, internet security is crucial to keeping that information safe. VPN protocols are the gateway to keeping your information secure and having one you can rely on will give you peace of mind in the long run.
Overview
Throughout this section, we’ll go through some VPN protocol products and services that can help you keep your information safe and secure.
Each VPN protocol has several features that will benefit you and your company. We’ll go through each one so you can narrow down your choice and find the right product for your business. Also, we’ll go through some common questions and phrases associated with VPN protocols. This will enable you to parse the language and come to a quality conclusion.
PPTP
Point-to-Point Tunneling Protocol is one of the oldest VPN protocols in existence. Microsoft designed and developed it in the mid-90’s. The overall design was designated for dial-up connections but with advanced technologies. PPTP’s basic encryption was rendered useless and easily cracked.
What it lacks in encryption it makes up for in speed. It offers some of the best connection speeds for users who might not need the ultra-heavy encryption that other businesses and companies desire. Many people have upgraded to other types of VPN protocols that are faster and more reliable products for this hyper day and age.
Highlights
- Ultra-fast speeds for streaming
- Almost all modern systems and devices support it
- Easy to set up and use
- Use for streaming and accessing geo-blocked content
Locations
PPTP, while an old VPN protocol, works almost anywhere and allows you to access geo-blocked content with speed and accuracy. Use it when you’re streaming or searching anywhere in the world to get the best information, quickly and efficiently.
Connections
PPTP connections work across platforms and include Windows, Linux, macOS, iOS, Android, and more. Each of these utilizes PPTP’s capability to use GRE or general routing encapsulation to form a primitive block for encryption.
Performance
PPTP works well if you only need minimal encryption but still want fast speeds. While it’s an older form of VPN protocol, it still works on a wide range of devices and connections. If you’re looking for heavy-duty encryption, this may not be the best product. With lower level encryption and security, it’s the biggest boost is the higher speeds you’ll be able to achieve. But even with that in mind, it continues to run well on Windows and other programs.
L2TP/IPSec

This is a step up from the PPTP protocol! Layer 2 Tunnel Protocol or L2TP doesn’t provide any encryption or privacy itself. Therefore, it is paired with security protocol IPsec which then makes it extremely secure and has no known vulnerabilities.
L2TP protocol is simply a tunneling protocol that creates a connection between you and a VPN server. Instead of providing the encryption itself, it relies on the IPSec program to encrypt your traffic and then keep it private and secure. Since L2TP doesn’t offer security at all and is simply a tunnel. It can be paired with any number of encryption protocols. Hence, it is flexible and easy to use.
Highlights
- Works well with several different encryption services
- Widely available with lots of support
Locations
You can use L2TP around the world to shop and perform online banking operations. While it is secure, it doesn’t have any clever ways to get through firewalls so they’re often used to block VPNs.
Connections
This protocol encapsulates your data twice which makes it useful but also a lot slower compared to other protocols on the market. Utilizing the other tools to encrypt traffic. This protocol to be very flexible when used with different types of connections.
Performance
This VPN protocol is a step up from PPTP but it does have some serious issues when it comes to working around firewalls. While it works well to securely shop online and perform banking operations, other types of connections and performance will be severely slowed down by the two-tier protection system offered by L2TP. It does work well if you want to connect a few company branches into one network and keep them all connected efficiently.
OpenVPN
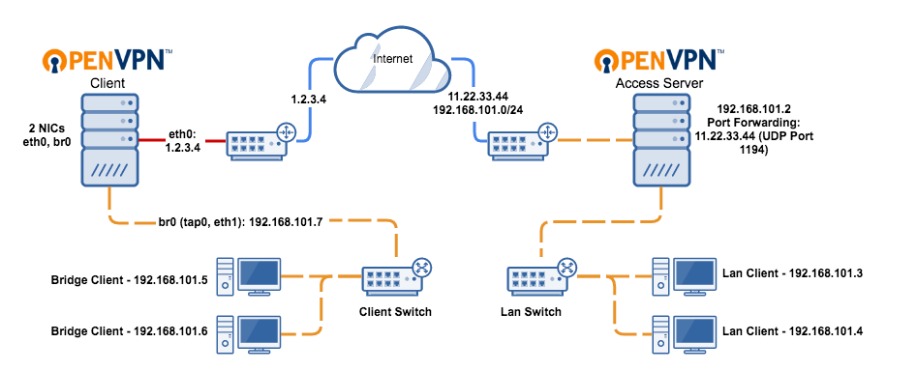
In another step forward for VPN protocols, OpenVPN works by allowing developers to utilize an open-source protocol that gives them access to the underlying code. It become popular in VPN communities. It offers virtually unbreakable AES-256 bit key encryption with 2048-bit RSA authentication.
Since this is an open-source algorithm, it offers some of the strongest encryption on the market. On the flip side, the speeds are severely hampered due to the higher levels of encryption offered to consumers. OpenVPN runs on either a TCP or UDP internet protocol.
Highlights
- Open source means the overall protocol is transparent.
- Can be checked for hidden backdoors or vulnerabilities
- Used with a wide array of different encryption
- Easily bypasses firewalls
- Offers top-level security in any situation or location
Locations
Since OpenVPN is open source and highly secure. It can be used in a wide range of locations. Hence, it allows you to keep your information safe even when on public WiFi.
Connections
OpenVPN works primarily with TCP or UDP Internet protocols to give you some of the highest levels of security on the market. It also runs nearly any encryption program you can think of so your experience is secure no matter where you are in the world. It easily bypasses the firewall regardless of the VPN you use and works even if you set up your VPN.
Performance
This is the protocol that any number of companies rely on to give their employees the security. Even if you’re using it a bit more casually when you find yourself scrolling the internet on public WiFi, it’s highly encrypted and keeps your data safe. With the open-source functionality, it gives everyone access to keep an eye out for bugs or other vulnerabilities that may be lurking in the code.
SSTP
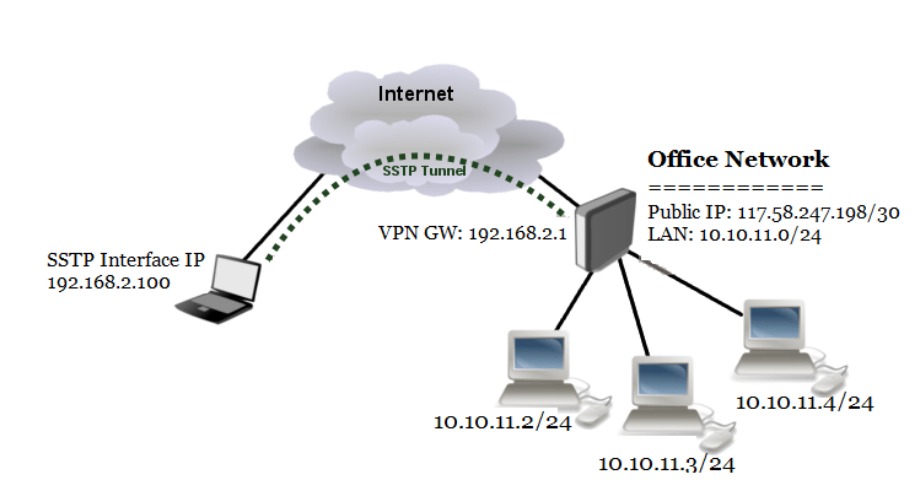
SSTP or Secure Socket Tunneling Protocol has become popular. It is integrated with every type of Microsoft operating system since early on in production. It utilizes 2048-bit SSL/TLS certificates when authenticating and 256-bit SSL keys for encryption. While it works across the board with Mircosoft-developed products, it is difficult to implement it elsewhere as developers have no access to the underlying code.
Microsoft as a company has been known to work with the NSA. The code is have some backdoors built-in. However, the developers don’t have access to the code itself. Hence, there’s no way for independent searchers to affirm whether it’s as secure as claimed.
Highlights
- Windows OS will have this built-in or easily accessible support
- Supports AES-256 encryption protocol
- Gets through most firewalls without interrupting communications
Locations
This can be used around the world as it is great for bypassing geo-restrictions. Also, it enhances your overall privacy while browsing the internet anywhere in the world.
Connections
This VPN protocol and tunneling system is one that works well with Microsoft and is easy to incorporate and install in any Windows OS system. The system itself is fairly secure and will keep your information safe and easily passes through firewalls. This tends to be a middle of the road system that works well but may have a few drawbacks for other types of systems on the market.
Performance
Overall, this is a middle of the road performing VPN protocol. There are a few questions about its security. Since it’s owned by Microsoft, third party security researchers often don’t have access to the code to double-check it for flaws or vulnerabilities. If you want a good VPN protocol that will help you bypass geo-restrictions and provide solid security for browsing the internet, this is a good choice!
IKEv2
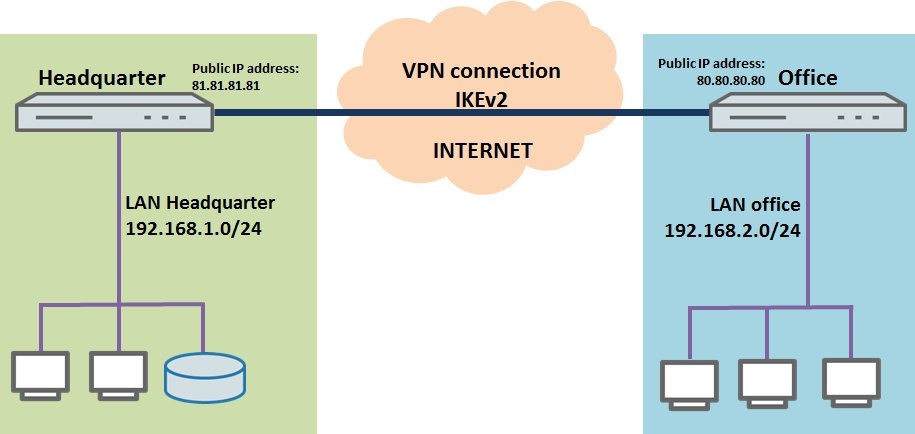
IKEv2 or Internet Key Exchange version 2, is a commonly used VPN tunneling protocol that offers up a secure key exchange session. It is paired with IPSec for encryption and authentication. It is very good at re-establishing the link after temporary connection loss. Also, this works well when switching connections across network types like when swapping from WiFi to cellular.
It is fast and secure. It excels at being stable. Throughout its uses, it utilizes, IPSec tools to give comprehensive VPN coverage no matter the connection.
Highlights
- Excellent stability when moving between internet connections
- Works with all of the leading encryption algorithms to make it a very secure VPN protocol
- Takes up only a little bandwidth when active
- NAT traversal makes it connect and communicate fast to get through firewalls
Locations
If you’re on the move, this is a great option! It quickly and efficiently switches from WiFi to mobile data and you won’t lose your overall VPN connection.
Connections
For Windows users, this is a great option. It works with each of their operating systems. Other types of operating systems may have a hard time getting IKEv2 to work on their operating systems. It will need adapted versions for anything outside of the Windows network.
Performance
The stability of the collaboration between IPSec and IKEv2 allows it to be used when moving between WiFi and mobile data. This makes it an ideal option for anyone on the move who needs stability and security along the way. While it works great with Windows operating systems, other types of systems will need an adapted version to make it work with other types of systems.
Common Terms
- VPN: Virtual Private Network
- AES: Advanced Encryption Standard
- Encryption: Anything involved in converting the data into the encrypted form so that hackers and threats can’t decipher what it means.
- Geo-restrictions: Streaming sites like Netflix and Amazon Prime are available worldwide. However, it has a slightly different content catalog depending on the country you’re streaming in. Using a VPN and VPN protocol, you can bypass these geo-restrictions to access those titles.
- Protocol: A set of security instructions for the VPN so it will know exactly how to deal with threats and keep you secure.
- Tunneling: The encrypted connection between your computer and the VPN server.
Frequently Asked Questions
Which VPN protocol is best?
This all depends on what exactly you want when it comes to security and encryption! Some types of VPN protocols are more secure but much slower than others. Others are fast but their encryption is thin. If you’re just casually surfing and using public WiFi, a less secure VPN protocol like PPTP is sufficient. If you need to encrypt and secure your entire company, you’ll want to go with something more secure like OpenVPN.
What is VPN in networking?
Using a VPN while networking keeps your data secure on your phone, computer, or tablet. This is no matter where you are in the world.
What is a VPN tunnel?
A VPN tunnel is the connection between your computer and the VPN server.
Takeaway
Every company or personal computer user has a different definition of a secure connection. Whether you want a fast connection with thinner encryption status or something with beefed up security for your whole company, you’ll need to choose the type of VPN protocol that works best for you. PPTP protocols are obsolete. However, it will still work providing thinner encryption but fast speeds for streaming. Others, like OpenVPN, give users a heavy-duty encryption status but slower speeds for streaming.
All VPN protocols are only as good as the VPN being used so be sure to pair them together wisely!